Your Website is Not a Static Brochure
We take pride in our commitment to keeping your information and services confidential, intact and available at all times. With iCandy Design, you can rest assured that your website and applications are protected end-to-end with the most advanced defence measures on the market.
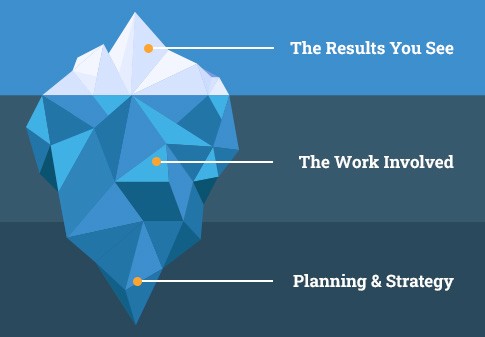
Many businesses treat their website like a glossy brochure: design it once, post it online and then walk away. "It looked great on launch day, so it must still be fine," the thinking goes. But a website is a living asset, a piece of technology that ages every single day and requires ongoing maintenance to stay secure and effective.
An outdated website can become an accessible point for those looking to exploit digital weaknesses. Old code and unpatched systems can leave your site vulnerable to attack, data compromise and exploitation. Recognising your website as a living asset that requires ongoing maintenance and proactive security updates is not just about safeguarding your data; it's about protecting your reputation and ensuring your online presence remains a secure and reliable asset for your business.
The Pillars of Our Approach
Our security practices are guided by the CIA triad, a widely accepted model for information security:
- Confidentiality: We protect your information from unauthorised access or disclosure, ensuring that sensitive data is only accessed by those with permission.
- Integrity: We ensure the information you and your customers receive is accurate and has not been tampered with. This includes using encryption and SSL certificates to protect data in transit.
- Availability: We ensure that authorised users have access to the information and systems they need when they need it, which is critical for business operations.
Our Technology: Built on Industry-Leading Infrastructure
To deliver on our promise of security and performance, we leverage a range of best-in-class technologies, including Cloudflare. With our website builds we ensure continued web security and performance, providing a critical layer of defence for your site by:
Why Partnering with a Digital Expert Matters
While implementing best practices in-house is vital, the complexity and evolving nature of digital threats often demand specialised expertise. This is where a partnership with a dedicated digital security expert becomes your "safe pair of hands."
At iCandy Design, we leverage industry-leading technologies and practices to ensure your online presence is not only functional but also highly secure and performant. Our commitment allows us to:
- Total Code Control: By carefully selecting and managing the software and frameworks we use, we maintain full oversight of every line of code. This minimises vulnerabilities often introduced by unvetted third-party plugins.
- Enhanced Security Protocols: With our own CMS, we have direct control over the underlying architecture and security measures. We can implement custom security protocols, monitor for unusual activity and respond swiftly to any potential digital incidents.
- Reduced Risk Exposure: By controlling our core systems, we minimise the "attack surface," which is the potential entry point for an attacker. This proactive approach creates a more secure environment for your digital assets.
- Tailored Solutions: Our in-house expertise allows us to offer more tailored and robust security solutions designed to protect your website and digital presence. We're not just offering generic advice; we're providing a secure foundation built from the ground up.
Beyond our core services, we empower your team with the knowledge to apply industry best practices, from using strong passwords and multi-factor authentication to regular software updates and employee training.
We are committed to not just delivering exceptional marketing but doing so on a secure and controlled platform, giving you peace of mind in an increasingly volatile digital world.
Frequently Asked Questions
What is a DDoS attack, and how do you protect me from it?
A DDoS (Distributed Denial of Service) attack is a malicious attempt to disrupt your website's normal traffic by overwhelming it with a flood of internet traffic. We use Cloudflare's vast global network to absorb and mitigate these attacks, stopping them before they can ever reach and disrupt your server.
Why can't I just build my website and leave it?
A website is more like a piece of technology than a static brochure. The code, plugins and connections age every day, and outdated systems can become vulnerable to attack. Ongoing security and maintenance are essential to protect your data, safeguard your reputation and ensure your site remains a secure and reliable asset for your business.
What is a WAF, and how does it benefit my business?
LA WAF, or Web Application Firewall, is a layer of defence that protects your website from common exploits. We deploy a WAF to actively block threats like SQL injection and cross-site scripting, ensuring that only legitimate traffic reaches your application and protecting your sensitive data from compromise.
How does your "Total Code Control" approach make my website more secure?
Our "Total Code Control" means we carefully manage the software and frameworks we use, maintaining full oversight of every line of code. This proactive approach allows us to minimize the vulnerabilities often introduced by unvetted third-party plugins and create a more secure environment for your digital assets.
We have our own internal IT team. Why would we need a security expert like iCandy Design?
While internal best practices are vital, the complexity of digital threats often demands specialized expertise. We provide a tailored, layered defence, leveraging industry-leading solutions and technologies like Cloudflare. Our in-house expertise allows us to provide a secure foundation built from the ground up, giving your team a reliable and robust platform to work on.